
In 2019, Test Impersonation Attacks
At SECOM, we perform many forms of social engineering attacks, from phishing to vishing and smishing as well as impersonation. All of these attacks are used regularly by actual attackers
2024 Training Schedule Available

At SECOM, we perform many forms of social engineering attacks, from phishing to vishing and smishing as well as impersonation. All of these attacks are used regularly by actual attackers

Watch Chris Hadnagy and other members of the Innocent Lives Foundation discuss what has been accomplished, the challenges, what’s next in the future of ILF, and help you see what your support, money and love has done to save children and catch predators.

Watch Social Engineer’s Ryan MacDougall and his journey on how he stepped outside an introverted personality to explore the world in a more successful way, but not without bumps and bruises which taught him valuable lessons
In today’s corporate world, security awareness training should be a common puzzle piece in general user onboarding and on-going staff education. With that training, regular testing should also be part
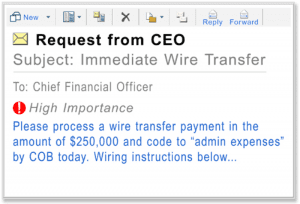
If you work for, or with, small to mid-sized companies, you may think the risk of social engineering attacks is lower for you. You know all 30-100 people in your

Enjoy the panel discussion from the SEVillage at DerbyCon8 with Chris Hadnagy, Chris Silvers, Rachel Tobac, Grifter and Jamison Scheeres about how one can stay ethical while being a professional social engineer.