
Learning from the MGM Security Breach
In the rapidly evolving digital landscape, no entity is immune to the pervasive threat of cyberattacks. The security breach at MGM Resorts highlights the vulnerability of even massive organizations. As
2024 State of Vishing Report
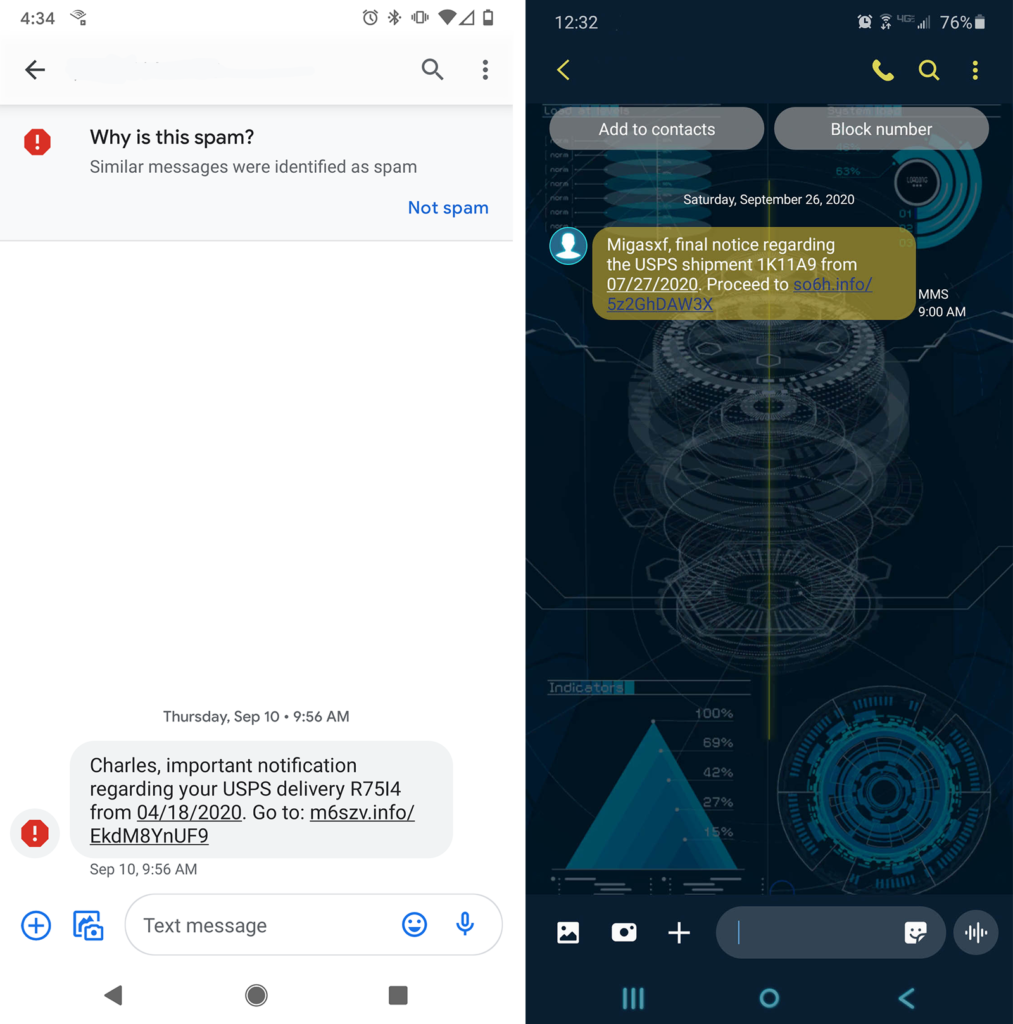
SMiShing can be defined as a form of phishing in which an attacker uses a text message to trick recipients into clicking a link, with the goal of collecting confidential information. A SMiSh may look something like this:
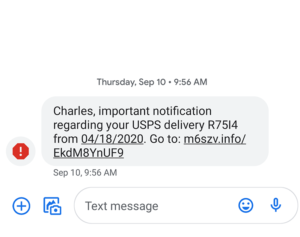
Other common SMiShing themes include Amazon delivery updates, utility alerts, and tax refunds. Regardless of the theme, these attacks include some common features. The attacker will try to inculcate a sense of urgency. In the above example, you can see that the attacker dubbed this notification as “urgent”. The message will also include a link the attacker wants you to click on. For an overview of techniques attackers may use in social engineering attacks, and what you can do to guard against them, check out one of our previous blogs here.
SafetyDetectives.com reports that losses from SMiShing alone can be hard to decipher because they contain links to phishing sites. However, the Internet Crime Complaint Center (IC3) reported over $44 million in losses from social engineering attacks in 2021 alone, including SMiShing. SMiShing based attacks specifically had reportedly risen 328% in 2020.
SMiShing recently made the news in August of 2022 when the popular communications provider, Twilio reported a data breach. The report provided by the company listed a “sophisticated social engineering attack designed to steal employee credentials” were the root cause of the breach. During the attack the adversaries created and sent out an SMS scam which impersonated Twilio’s IT department. It warned employees that their passwords had expired or needed to be changed. Employees who clicked on the link were taken to a spoofed version of the Twilio sign-in page where their login credentials were harvested. Those credentials allowed the attackers to access the company’s internal systems and view the data of customers. Due to the breach, Signal, a company with the reputation of providing secure communications, also reported that it exposed the phone number and SMS of codes of over 1,900 of their customers.
As seen, SMiShing is something we should all be on the lookout for. It isn’t only your personal data that is at risk. Proprietary company data can be in danger if company emails, or other company information, is stored on your personal device. Through SMiShing, attackers may be able to gain access to your device and its information. This is why it is so important that we are aware of this attack vector. The best way to protect against these types of scams is to not open messages or links that seem suspicious to you. Here are some additional tips to help keep you safe:
So, how can you keep your company safe? Consider training employees with a Managed SMiShing Service program. Similar to Phishing or Vishing programs, SMiShing training will focus on getting your employees used to dealing with SMiShing attacks. It will do this by giving them firsthand experience of what a SMiSh really is, what it may look like, and understand the proper process to shut down and report the attack. Experience really is the best trainer.
Images:
https://www.thesslstore.com/blog/what-is-smishing-definition-examples-protection-tips/
https://content.gallup.com/origin/gallupinc/Gallup-Spaces/Production/Cms/WORKPLACEV9CMS/

In the rapidly evolving digital landscape, no entity is immune to the pervasive threat of cyberattacks. The security breach at MGM Resorts highlights the vulnerability of even massive organizations. As

SMiShing Attacks in the News In February 2024, 19.2 billion spam texts bombarded U.S citizens according to a recent report. As annoying as spam texts are, they are not always