
Learning from the MGM Security Breach
In the rapidly evolving digital landscape, no entity is immune to the pervasive threat of cyberattacks. The security breach at MGM Resorts highlights the vulnerability of even massive organizations. As
2024 State of Vishing Report

SMiShing uses SMS (Short Message Service) as the attack vector. The attacker’s objective is to trick the target into installing malware on their device, or to reveal account information. The attacker crafts a SMiShing message to make the receiver think the communication is from a familiar or trusted source. The bad actor then sends their target a SMiShing message containing a malicious link. The link, if clicked, redirects the target to a website under the attacker’s control. SMiShing is a social engineering attack because criminals exploit the target’s vulnerabilities; the desire to trust, to be helpful, or to act quickly on a perceived danger. SMiShing is a very real security threat to enterprises as 39% of employees now access corporate data on personal devices.
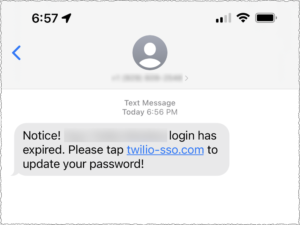
SMiShing attack on Twilio employees’ compromises employee and customer accounts. On August 4, 2022, Twilio became aware of unauthorized access to information related to a limited number of Twilio customer accounts. How did the attackers gain access? According to Twilio’s Incident Report, current and former employees received text messages purporting to be from Twilio’s IT (Information Technology) department. The SMiShing message suggested that the employees’ passwords had expired, or that their schedule had changed. The SMiShing message included a link that when clicked would take the employee to a URL (Uniform Resource Locator) controlled by the attackers. The URLs used words including “Twilio,” “Okta,” and “SSO” to trick the employees. If they clicked on the link, it would take them to a webpage that impersonated Twilio’s sign-in page.
The attack on Twilio highlights how malicious actors threaten information security by focusing their attacks on company employees. Are your employees trained to identify SMiShing attacks? Social-Engineer’s Managed SMiShing Service is designed to test, educate, and protect your human network. We apply scientifically proven methodologies to uncover vulnerabilities, define risk, and provide remediation. Our fully managed program measures and tracks how employees respond to SMiShing attacks with data driven targeting and training.
Please contact us today for a consultation.

In the rapidly evolving digital landscape, no entity is immune to the pervasive threat of cyberattacks. The security breach at MGM Resorts highlights the vulnerability of even massive organizations. As

SMiShing Attacks in the News In February 2024, 19.2 billion spam texts bombarded U.S citizens according to a recent report. As annoying as spam texts are, they are not always