
Practical Steps to Avoid Deepfakes
In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital
Join us for the Human Behavior Conference on Oct. 30th


The much anticipated 2017 Verizon DBIR was recently released and has some interesting data for social engineering attacks in 2016. Social-Engineer is proud to have been a contributor to this year’s report. Below are highlights from the report, and some tips at the end on how to stay safe.

Verizon studied 42,068 security incidents that resulted in 1,935 breaches. Overall, 43% of the documented breaches involved social engineering attacks! That’s almost half, and these are the only representative of the reported/documented breaches.
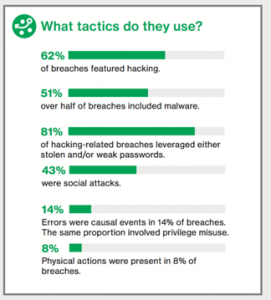
Figure 1: Overall breaches using Social Attacks
Not surprisingly, 66% of malware came from malicious email attachments. These could have been emails from phishing attacks or may have come from a trusted account that had been previously hacked. Either way, the majority of the malware infections started from a rotten email.
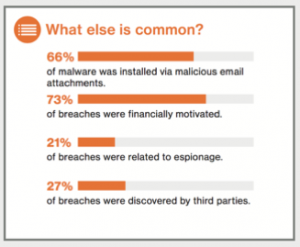
Figure 2: Malware and phishing are close friends
The Education sector saw another rise in social engineering attacks. Over half of the breaches involved the theft of Personally Identifiable Information (PII) of students and teachers, and just over 25% resulted in the loss of intellectual property. Social engineering attacks (mostly phishing) were used in almost 44% of these breaches and were combined with another attack vector in many cases.
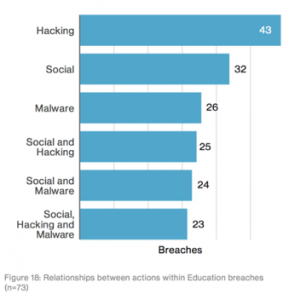
Figure 3: Social attacks against the Education sector
The Information sector (social media, telecommunications, software) saw phishing involved in most attacks. Once clicked, the malicious emails often installed malware to collect credentials and carry out further hacking against the target.

Figure 4: Phishing took place in most attacks against the Information sector
The Manufacturing sector was hit particularly hard last year, with the majority of breaches managing to snag proprietary data from the target. Similar to the Information sector, phishy emails were the gateway for malware to be installed in 73% of these incidents!
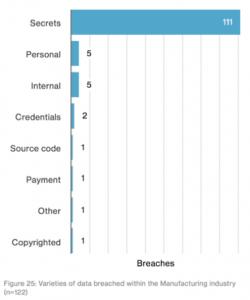
Figure 5: Phishing was involved in 73% of these breaches
Espionage attacks driven by state-affiliated actors preferred phishing as their main source of starting an attack. Manufacturing again was at the top of the attacked industry list.

Figure 6: The spy who phished me
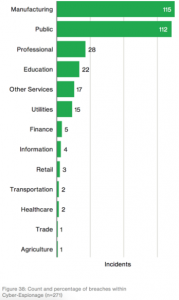
Figure 7: Industries targeted by state-affiliated actors
Looking at simulated phishing exercises, no industry was immune from clicking on malicious links. Manufacturing seemed to be the most vulnerable, but other industries from Healthcare to Education were also susceptible. This goes to show that continual training on spotting and reporting phishing emails is critical to your business.
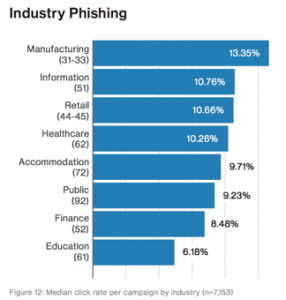
Figure 8: Simulated phishing results across the industry
Staying Safe From Social Engineering Attacks
Per Verizon: “Our data is non-exclusively multinomial meaning a single feature, such as “Action”, can have multiple values (i.e., “social”, “malware” and “hacking”). This means that percentages do not necessarily add up to 100%. For example, if there are five botnet breaches, the sample size is five. However, since each botnet used phishing, installed keyloggers and used stolen credentials, there would be five social actions, five hacking actions, and five malware actions—adding up to 300%. This is normal, expected and handled correctly in our analysis and tooling.”
Sources: https://enterprise.verizon.com/resources/reports/2017_dbir.pdf

In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital

According to Workplace, in 2019, “60% of remote-capable employees spent their week working fully on-site, whereas that figure has fallen to just 20% in 2023.” Additionally, hybrid work has increased