
Practical Steps to Avoid Deepfakes
In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital
Join us for the Human Behavior Conference on Oct. 30th
Phishing reached an all-time high in the first quarter of 2022. To clarify what this means, in the first quarter of 2022 there were more than one million attacks. Without a doubt this is the worst quarter for phishing the Anti-Phishing Working Group (APWG) have ever observed. Here are a few significant trends they report on:
Check Point Technologies reported on another equally important statistic that the business social network LinkedIn was related to over 52% of all phishing schemes globally in the first quarter of 2022.
At Social-Engineer, we define phishing as the “practice of sending emails appearing to be from reputable sources with the goal of influencing or gaining personal information.”
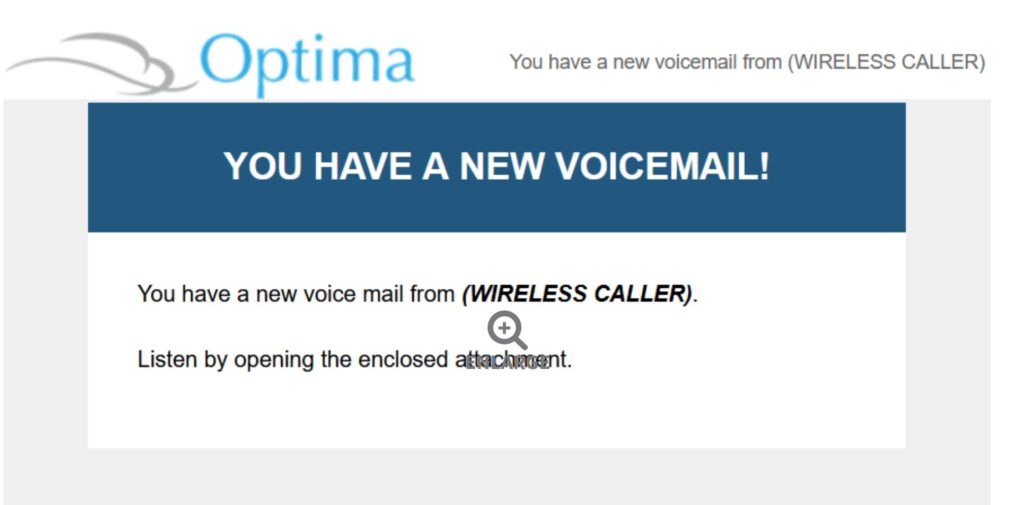
Malicious Voicemail-Notification-Themed Emails Attempt to Steal Office365 and Outlook Credentials.
In this recent campaign, threat actors are targeting users in US-based organizations such as software security, US military, security solution providers, healthcare/pharmaceutical, and the manufacturing supply chain. Researchers at Zscaler’s ThreatLabz, say that the attack begins with an email telling the targeted user they have a voicemail waiting for them contained in an attachment. If the user falls for the lure and opens the attachment it will direct them to a credential phishing site posing as a legitimate Microsoft sign-in page. Once the target is on the phony sign-in page they receive instructions to login, and complete the download of the voicemail recording. If the target does so, they will in fact be handing over their username and password to criminals.
Image: Zscaler’s ThreatLabz
To make the phishing email even more convincing, the bad actor crafts the “from” field to include the name of the target company. For instance, when an employee at Zscaler ThreatLabz was targeted the page URL used the format: zscaler.zscaler.briccorp[.]com/. Zscaler’s ThreatLabz reports on a few key findings of this phishing campaign:
How would your employees respond if they became a target in a credential theft campaign? Would they recognize the phishing email? Would they report it? Equally important, can your company afford the potential damage resulting from user credentials in the hands of criminals?
As shown above, phishing is an attack vector that criminals are exploiting with devastating results. In view of this, we invite you to explore Social-Engineer’s Managed Phishing Service. This is a fully managed program that measures and tracks how employees respond to email phishing attacks. Our Managed Phishing Service provides the following features:
Our patented process to construct messaging on varying levels of sophistication identifies at-risk user groups. Employees also demonstrate their ability to recognize and report fraudulent emails. Act now to protect your company from the accelerating risk of phishing emails. Please contact us without delay to schedule a consultation.

In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital

According to Workplace, in 2019, “60% of remote-capable employees spent their week working fully on-site, whereas that figure has fallen to just 20% in 2023.” Additionally, hybrid work has increased