In August 2023, The Office of Information Security and Health Sector Cybersecurity Coordination Center (HC3) issued a report warning hospitals about the rising threat of SMiShing attacks targeting the healthcare sector.
SMiShing: phishing via SMS (short message service) text message
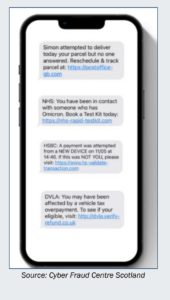
Why is the healthcare sector experiencing an uptick in SMiShing attacks? The HC3 report notes that users are much more trusting of text messages. The report goes on to say that not as many people are aware of the dangers of clicking links in text messages. So SMiShing is often lucrative to attackers searching for credentials, banking information and confidential data. Criminals use psychological tactics in their text messages to gain access to hospital and healthcare IT (Information Technology) networks. The text messages will usually create a sense of urgency or fear. The HC3 report says to be on the lookout for the following types of text messages:
- Deadlines and time-sensitive language
- Scarcity
- A quick fix
Screenshot: HC3 Multi-factor Authentication & Smishing Report, August 10, 2023
At an average cost of USD 10.93 million, healthcare has the highest data breach costs of all industries. What can the health sector do to protect itself? The HC3 recommends that all health sector employees add MFA (Multifactor Authentication) to all devices. We agree that this is a vital security protocol to implement. But is there more that the health sector can do to protect itself from SMiShing attacks?
Social-Engineer’s Managed SMiShing Service
While MFA is a key step towards protection, SMiShing testing and education within the healthcare sector is vital. Why do we say that? Because MFA alone will not protect against the psychological tactics and social engineering techniques that criminals use in a SMiShing attack.
Test. Educate. Protect.
With our Managed SMiShing Service you’ll receive a fully managed program that measures and tracks how your employees respond to text-based phishing attacks on corporate managed SMS-capable devices. Your employees will learn what a SMiShing message looks like and how to report it safely. As a first step, we recommend updating your BYOD (Bring Your Own Device) policy and establishing a reporting process for employees to submit suspicious text messages for review by your security team. Once you are ready, we invite you to partner with us for testing and education that will help protect your employees against SMiShing attacks.
You May Also Like
Phishing Attacks Targeting the Healthcare Sector
Vishing Attacks Targeting the Healthcare Sector