
Practical Steps to Avoid Deepfakes
In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital
Join us for the Human Behavior Conference on Oct. 30th

Employees are increasingly accessing corporate information and accounts from their personal phones. As a result, SMiShing attacks now pose a serious threat to corporate information. How serious is this threat? Consider this statistic; 20% of energy industry employees were exposed to a mobile phishing attack in the first half of 2021. That is a 161% increase from the second half of 2020. Across the board, companies lost an alarming $54,241,075 because of social attacks including SMiShing according to the 2020 FBI Internet Crime Complaint Center report.
The word SMiShing comes from combining SMS (Short Message Service), the technology behind texting, with phishing, the practice of stealing personal or financial information through deceptive emails. Basically, SMiShing is phishing but by another means, namely text messages on mobile devices.

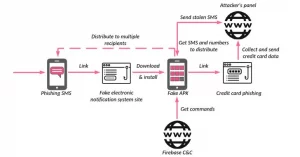
Image: https://thehackernews.com/2021/12/researchers-warn-iranian-users-of.html
Your company’s best defense is to educate employees and ensure they understand the threats posed by SMiShing attacks. The Social-Engineer Teaming Service is a valuable tool that enables organizations to evaluate their unique attack surface to social engineering attacks. Upon request, we can include a SMiShing part to our SE (Social-Engineer) Teaming Service engagement. This will test your organization’s human network for their understanding of policies relating to SMS attacks.

In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital

According to Workplace, in 2019, “60% of remote-capable employees spent their week working fully on-site, whereas that figure has fallen to just 20% in 2023.” Additionally, hybrid work has increased