
Practical Steps to Avoid Deepfakes
In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital
Join us for the Human Behavior Conference on Oct. 30th

A direct deposit scam is a type of business email compromise or email account compromise (BEC/EAC) scheme. Widely prevalent, these scams affect industries in all sectors. In fact, in 2019, the FBI’s Internet Crime Complaint Center (IC3) received 23,775 reports of BEC/EAC scams with adjusted losses of $1.7 billion. Notably, according to the report there was also a dramatic uptick in direct deposit BEC/EAC scams. Clearly, this is a scam that organizations need to be aware of.
Does your company use direct deposit for payroll? Because of the savings associated with direct deposit many companies do. As an employee, I love the convenience of direct deposit. It gives me quick access to my paycheck as well as the convenience of skipping the ATM and/or bank queue. And, for me that’s a huge plus while coping with the coronavirus pandemic. However, in view of the FBI’s findings, organizations need to take this scam seriously and implement security strategies to protect themselves. In this month’s blog, we’ll examine how direct deposit scams work, what to do if you’ve been scammed, and how to protect your company from direct deposit scams.

This type of scheme uses social engineering tactics, such as impersonation and manipulation. As seen in previous versions of direct deposit scams, cybercriminals would pose as Human Resource (HR) staff and contact employees seeking payroll information via phishing emails. However, in the newest variation, bad actors have reversed roles. Now, they are posing as the employees. And typically, high value employees such as the CEO or CFO. They then contact HR staff via email, requesting changes to their direct deposit information.
What makes this scam so dangerous? First, in this new variation, the emails easily bypass technical controls for malicious communications. Why is this so? Because the phishing emails contain no request for money, no glaring spelling mistakes, and they’re short and friendly. I’ll talk more on this later. Additionally, bad actors are using free email services such as Gmail. They simply create a new account using the employee’s name. By doing so they circumvent tools designed to detect hacking attempts on employee email.
Second, the phishing emails manipulate emotions. The bad actor crafts the email specifically to create a sense of urgency. For example, posing as the CEO, the cybercriminal may request a change to their direct deposit information that must happen before the processing of the next payroll. If the HR employee replies and offers to help, the bad actor sends new bank routing information. The paycheck is then deposited in the cybercriminal’s account. As a result, the employee is stuck waiting for a replacement paycheck, the company is liable for the stolen funds, and the bad actor gets money for nothing. A bad scenario by anyone’s definition.
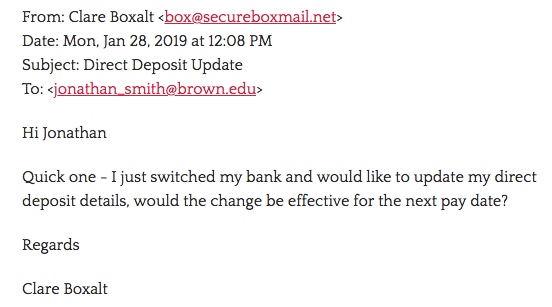
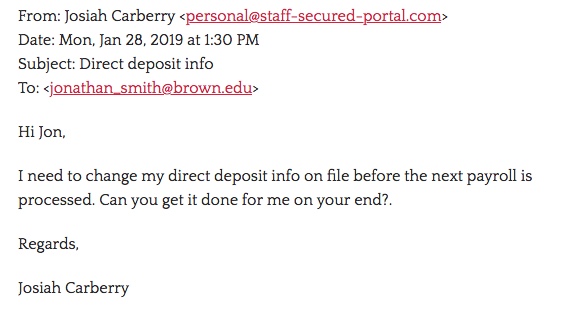
Are you curious what these emails look like? Here’s a couple of examples of direct deposit phishing emails sent to Brown University.
What should you do if your company has been scammed? It’s important to react promptly and purposefully. The FBI’s Internet Crime Complaint Center recommends taking these actions:
Nobody wants to experience the anxiety, frustration, and financial loss from direct deposit scams. So, as an organization, take steps to strengthen your security posture. What can you do? Security training that focuses on the human element is a must!
To protect your organization from direct deposit scams as well as other cybercrimes, intrusion detection systems, firewalls and other devices to monitor your network are important. However, it’s absolutely vital not to overlook the human element in your security strategy. For instance, in direct deposit scams, cybercriminals target people, not networks. Which brings me back to an earlier point. In these recent direct deposit scams, bad actors are crafting emails that bypass technical controls. Clearly, training employees to understand and recognize malicious social engineering tactics is important. To that end, we recommend a Social Engineering Risk Assessment. Your organization will receive expert analysis of your potential risk, enabling you to plan, educate, and prepare for a social engineering attack.
Implementing phishing training such as Phishing as a Service® (PHaaS®) is also a must. PHaaS® training raises employee awareness and provides education. It also gives your organization a continuous repeatable process for accessing phishing risks.
As millions transition to working remotely because of the coronavirus, here’s a few basic best practices mentioned in the Social-Engineer.org April Newsletter that can strengthen your organization’s security:
As cybercriminals adapt and create new twists to old scams, we must adopt and adapt new security strategies as well. Now’s the time to implement security training that includes the human element! Social-Engineer, LLC can help!
Sources:
https://pdf.ic3.gov/2019_IC3Report.pdf/
https://www.social-engineer.com/
https://it.brown.edu/alerts/read/request-change-direct-deposit-information
https://www.social-engineer.com/services/
https://www.cnbc.com/2019/04/09/new-wire-fraud-scam-targets-your-direct-deposit-info-paycheck.html
https://www.ic3.gov/default.aspx
https://www.social-engineer.com/social-engineering-risk-assessment/
https://www.social-engineer.com/phishing-as-a-service-phaas/
Image:
https://its.uiowa.edu/news/it-security-office-warns-work-home-schemes

In the modern era of technology, the methods of cyber criminals and bad actors alike continue to evolve. The topic of deepfake attacks is becoming more common in the digital

According to Workplace, in 2019, “60% of remote-capable employees spent their week working fully on-site, whereas that figure has fallen to just 20% in 2023.” Additionally, hybrid work has increased