
The Point (and Click) of Phishing Exercises
When we speak with companies about performing phishing tests, one of the most common responses is “We know a lot of people will click, so why bother?” There are two
2024 State of Vishing Report

When we speak with companies about performing phishing tests, one of the most common responses is “We know a lot of people will click, so why bother?” There are two

SMiShing uses SMS (Short Message Service) as the attack vector. The attacker’s objective is to trick the target into installing malware on their device, or to reveal account information. The

Vishing, a word that was entered into the Oxford Dictionary in 2015, defines what we call “voice phishing”. Using the telephone to phish information from targets could lead to network,
When you are a vendor who provides a valuable service, you look for opportunities to help companies. Sometimes, a vendor’s claims can be exaggerated or even contrived. For that reason,

A new report by Mutare reveals costly and pervasive shortcomings in enterprise security protections against voice network attacks, such as vishing, robocalls, and spoof calls. Significantly, nearly half (47%) of
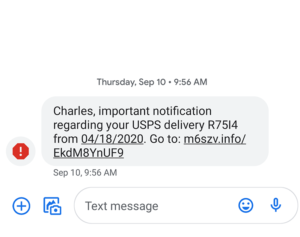
SMiShing can be defined as a form of phishing in which an attacker uses a text message to trick recipients into clicking a link, with the goal of collecting confidential